Rotate Your SSL/TLS Certificates Now – Amazon RDS and Amazon Aurora Expire in 2024
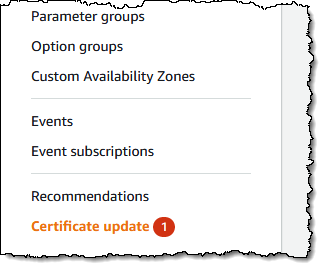 Don’t be surprised if you have seen the Certificate Update in the Amazon Relational Database Service (Amazon RDS) console.
Don’t be surprised if you have seen the Certificate Update in the Amazon Relational Database Service (Amazon RDS) console.
If you use or plan to use Secure Sockets Layer (SSL) or Transport Layer Security (TLS) with certificate verification to connect to your database instances of Amazon RDS for MySQL, MariaDB, SQL Server, Oracle, PostgreSQL, and Amazon Aurora, it means you should rotate new certificate authority (CA) certificates in both your DB instances and application before the root certificate expires.
Most SSL/TLS certificates (rds-ca-2019) for your DB instances will expire in 2024 after the certificate update in 2020. In December 2022, we released new CA certificates that are valid for 40 years (rds-ca-rsa2048-g1) and 100 years (rds-ca-rsa4096-g1 and rds-ca-ecc384-g1). So, if you rotate your CA certificates, you don’t need to do It again for a long time.
Here is a list of affected Regions and their expiration dates of rds-ca-2019:
| Expiration Date | Regions |
| May 8, 2024 | Middle East (Bahrain) |
| August 22, 2024 | US East (Ohio), US East (N. Virginia), US West (N. California), US West (Oregon), Asia Pacific (Mumbai), Asia Pacific (Osaka), Asia Pacific (Seoul), Asia Pacific (Singapore), Asia Pacific (Sydney), Asia Pacific (Tokyo), Canada (Central), Europe (Frankfurt), Europe (Ireland), Europe (London), Europe (Paris), Europe (Stockholm), and South America (São Paulo) |
| September 9, 2024 | China (Beijing), China (Ningxia) |
| October 26, 2024 | Africa (Cape Town) |
| October 28, 2024 | Europe (Milan) |
| Not affected until 2061 | Asia Pacific (Hong Kong), Asia Pacific (Hyderabad), Asia Pacific (Jakarta), Asia Pacific (Melbourne), Europe (Spain), Europe (Zurich), Israel (Tel Aviv), Middle East (UAE), AWS GovCloud (US-East), and AWS GovCloud (US-West) |
The following steps demonstrate how to rotate your certificates to maintain connectivity from your application to your database instances.
Step 1 – Identify your impacted Amazon RDS resources
As I said, you can identify the total number of affected DB instances in the Certificate update page of the Amazon RDS console and see all of your affected DB instances. Note: This page only shows the DB instances for the current Region. If you have DB instances in more than one Region, check the certificate update page in each Region to see all DB instances with old SSL/TLS certificates.

You can also use AWS Command Line Interface (AWS CLI) to call describe-db-instances to find instances that use the expiring CA. The query will show a list of RDS instances in your account and us-east-1 Region.
$ aws rds describe-db-instances --region us-east-1 |
jq -r '.DBInstances[] |
select ((.CACertificateIdentifier != "rds-ca-rsa2048-g1") and
(.CACertificateIdentifier != "rds-ca-rsa4096-g1") and
(.CACertificateIdentifier != "rds-ca-ecc384-g1")) |
"DBInstanceIdentifier:
(.DBInstanceIdentifier), CACertificateIdentifier:
(.CACertificateIdentifier)"'Step 2 – Updating your database clients and applications
Before applying the new certificate on your DB instances, you should update the trust store of any clients and applications that use SSL/TLS and the server certificate to connect. There’s currently no easy method from your DB instances themselves to determine if your applications require certificate verification as a prerequisite to connect. The only option here is to inspect your applications’ source code or configuration files.
Although the DB engine-specific documentation outlines what to look for in most common database connectivity interfaces, we strongly recommend you work with your application developers to determine whether certificate verification is used and the correct way to update the client applications’ SSL/TLS certificates for your specific applications.
To update certificates for your application, you can use the new certificate bundle that contains certificates for both the old and new CA so you can upgrade your application safely and maintain connectivity during the transition period.
For information about checking for SSL/TLS connections and updating applications for each DB engine, see the following topics:
- Updating applications to connect to MariaDB instances using new SSL/TLS certificates
- Updating applications to connect to Microsoft SQL Server DB instances using new SSL/TLS certificates
- Updating applications to connect to MySQL DB instances using new SSL/TLS certificates
- Updating applications to connect to Oracle DB instances using new SSL/TLS certificates
- Updating applications to connect to PostgreSQL DB instances using new SSL/TLS certificates
- Updating applications to connect to Aurora MySQL DB clusters using new SSL/TLS certificates.
- Updating applications to connect to Aurora PostgreSQL DB clusters using new SSL/TLS certificates.
Step 3 – Test CA rotation on a non-production RDS instance
If you have updated new certificates in all your trust stores, you should test with a RDS instance in non-production. Do this set up in a development environment with the same database engine and version as your production environment. This test environment should also be deployed with the same code and configurations as production.
To rotate a new certificate in your test database instance, choose Modify for the DB instance that you want to modify in the Amazon RDS console.

In the Connectivity section, choose rds-ca-rsa2048-g1.

Choose Continue to check the summary of modifications. If you want to apply the changes immediately, choose Apply immediately.
To use the AWS CLI to change the CA from rds-ca-2019 to rds-ca-rsa2048-g1 for a DB instance, call the modify-db-instance command and specify the DB instance identifier with the --ca-certificate-identifier option.
$ aws rds modify-db-instance \
--db-instance-identifier <mydbinstance> \
--ca-certificate-identifier rds-ca-rsa2048-g1 \
--apply-immediatelyThis is the same way to rotate new certificates manually in the production database instances. Make sure your application reconnects without any issues using SSL/TLS after the rotation using the trust store or CA certificate bundle you referenced.
When you create a new DB instance, the default CA is still rds-ca-2019 until January 25, 2024, when it will be changed to rds-ca-rsa2048-g1. For setting the new CA to create a new DB instance, you can set up a CA override to ensure all new instance launches use the CA of your choice.
$ aws rds modify-certificates \
--certificate-identifier rds-ca-rsa2048-g1 \
--region <region name>You should do this in all the Regions where you have RDS DB instances.
Step 4 – Safely update your production RDS instances
After you’ve completed testing in non production environment, you can start the rotation of your RDS databases CA certificates in your production environment. You can rotate your DB instance manually as shown in Step 3. It’s worth noting that many of the modern engines do not require a restart, but it’s still a good idea to schedule it in your maintenance window.
In the Certificate update page of Step 1, choose the DB instance you want to rotate. By choosing Schedule, you can schedule the certificate rotation for your next maintenance window. By choosing Apply now, you can apply the rotation immediately.

If you choose Schedule, you’re prompted to confirm the certificate rotation. This prompt also states the scheduled window for your update.

After your certificate is updated (either immediately or during the maintenance window), you should ensure that the database and the application continue to work as expected.
Most of modern DB engines do not require restarting your database to update the certificate. If you don’t want to restart the database just for CA update, you can use the --no-certificate-rotation-restart flag in the modify-db-instance command.
$ aws rds modify-db-instance \
--db-instance-identifier <mydbinstance> \
--ca-certificate-identifier rds-ca-rsa2048-g1 \
--no-certificate-rotation-restartTo check if your engine requires a restart you can check the SupportsCertificateRotationWithoutRestart field in the output of the describe-db-engine-versions command. You can use this command to see which engines support rotations without restart:
$ aws rds describe-db-engine-versions \
--engine <engine> --include-all --region <region> |
jq -r '.DBEngineVersions[] |
"EngineName: (.Engine),
EngineVersion: (.EngineVersion),
SupportsCertificateRotationWithoutRestart: (.SupportsCertificateRotationWithoutRestart),
SupportedCAs: ([.SupportedCACertificateIdentifiers |
join(", ")])"'Even if you don’t use SSL/TLS for the database instances, I recommend to rotate your CA. You may need to use SSL/TLS in the future, and some database connectors like the JDBC and ODBC connectors check for a valid cert before connecting and using an expired CA can prevent you from doing that.
To learn about updating your certificate by modifying your DB instance manually, automatic server certificate rotation, and finding a sample script for importing certificates into your trust store, see the Amazon RDS User Guide or the Amazon Aurora User Guide.
Things to Know
Here are a couple of important things to know:
- Amazon RDS Proxy and Amazon Aurora Serverless use certificates from the AWS Certificate Manager (ACM). If you’re using Amazon RDS Proxy when you rotate your SSL/TLS certificate, you don’t need to update applications that use Amazon RDS Proxy connections. If you’re using Aurora Serverless, rotating your SSL/TLS certificate isn’t required.
- Now through January 25, 2024 – new RDS DB instances will have the
rds-ca-2019certificate by default, unless you specify a different CA via theca-certificate-identifieroption on thecreate-db-instanceAPI; or you specify a default CA override for your account like mentioned in the above section. Starting January 26, 2024 – any new database instances will default to using therds-ca-rsa2048-g1certificate. If you wish for new instances to use a different certificate, you can specify which certificate to use with the AWS console or the AWS CLI. For more information, see thecreate-db-instanceAPI documentation. - Except for Amazon RDS for SQL Server, most modern RDS and Aurora engines support certificate rotation without a database restart in the latest versions. Call
describe-db-engine-versionsand check for the response fieldSupportsCertificateRotationWithoutRestart. If this field is set totrue, then your instance will not require a database restart for CA update. If set tofalse, a restart will be required. For more information, see Setting the CA for your database in the AWS documentation. - Your rotated CA signs the DB server certificate, which is installed on each DB instance. The DB server certificate identifies the DB instance as a trusted server. The validity of DB server certificate depends on the DB engine and version either 1 year or 3 year. If your CA supports automatic server certificate rotation, RDS automatically handles the rotation of the DB server certificate too. For more information about DB server certificate rotation, see Automatic server certificate rotation in the AWS documentation.
- You can choose to use the 40-year validity certificate (
rds-ca-rsa2048-g1) or the 100-year certificates. The expiring CA used by your RDS instance uses the RSA2048 key algorithm and SHA256 signing algorithm. Therds-ca-rsa2048-g1uses the exact same configuration and therefore is best suited for compatibility. The 100-year certificates (rds-ca-rsa4096-g1andrds-ca-ecc384-g1) use more secure encryption schemes thanrds-ca-rsa2048-g1. If you want to use them, you should test well in pre-production environments to double-check that your database client and server support the necessary encryption schemes in your Region.
Just Do It Now!
Even if you have one year left until your certificate expires, you should start planning with your team. Updating SSL/TLS certificate may require restart your DB instance before the expiration date. We strongly recommend that you schedule your applications to be updated before the expiry date and run tests on a staging or pre-production database environment before completing these steps in a production environments. To learn more about updating SSL/TLS certificates, see Amazon RDS User Guide and Amazon Aurora User Guide.
If you don’t use SSL/TLS connections, please note that database security best practices are to use SSL/TLS connectivity and to request certificate verification as part of the connection authentication process. To learn more about using SSL/TLS to encrypt a connection to your DB instance, see Amazon RDS User Guide and Amazon Aurora User Guide.
If you have questions or issues, contact your usual AWS Support by your Support plan.
— Channy